Analysis

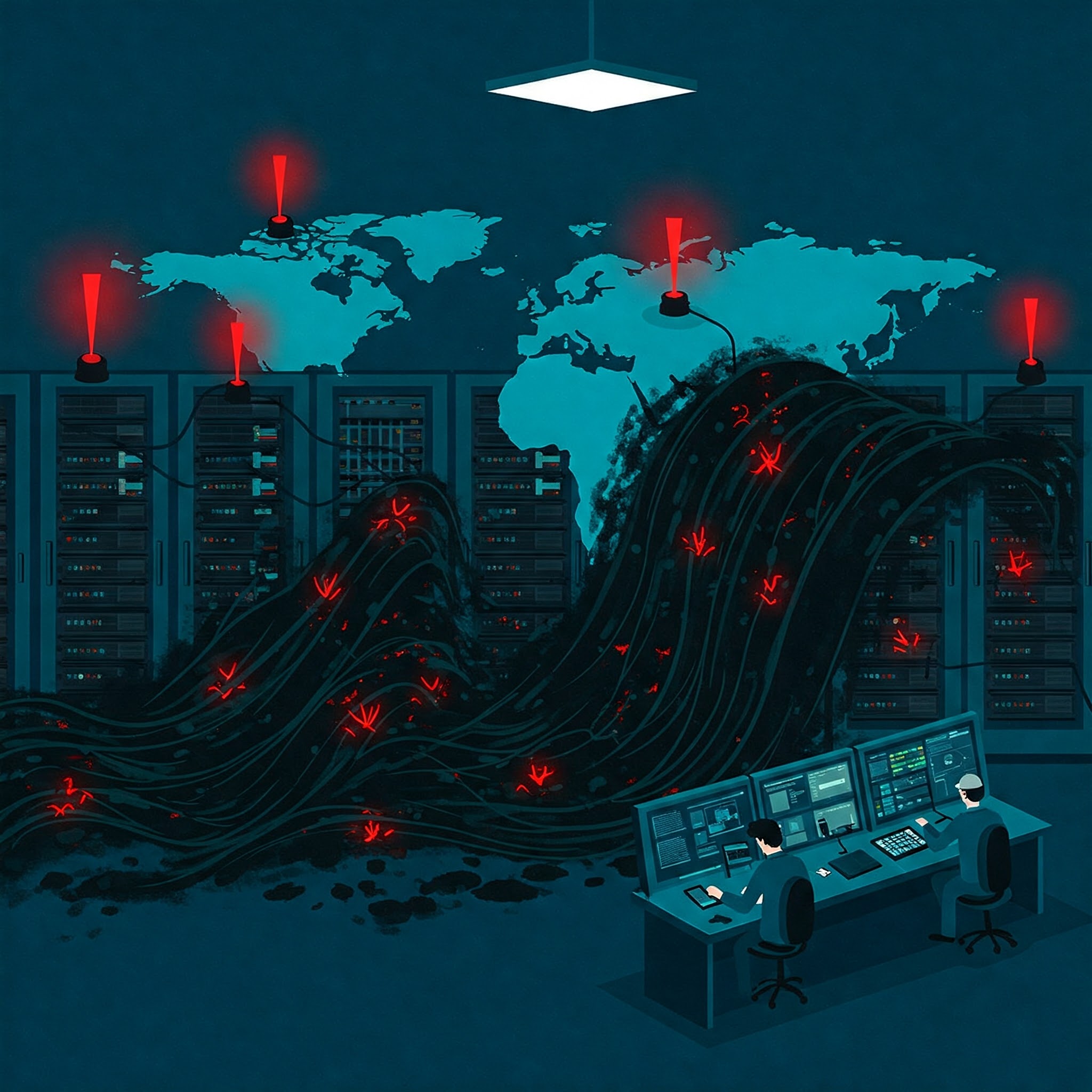
A Multi-Front War in Cyber Security
The Rise of Advanced, Multi-Stage Attacks: Several reports highlight the increasing complexity of cyberattacks. We&rsquo...
Large-scale Cyberattack Targets Internet Service Providers
Large-scale cyberattack targets internet service providers (ISPs) was a coordinated assault, primarily impacting network...

VMware ESXi Vulnerabilities Fuel Ransomware Attacks
Recently, there has been a surge in cybersecurity incidents exploiting VMware ESXi vulnerabilities. Tens of thousands of...
This Week in Cybersecurity: A Critical Review for IT Leaders and Security Professionals
This week saw a concerning surge in significant cybersecurity incidents, impacting various sectors and highlighting pers...

The AI-Powered Ransomware Surge: Are Cybercriminals Getting Lazier or Smarter?
Recently we have seen threat actor tactics shifting towards an escalated use of artificial intelligence (AI) to enhance ...

BADBOX 2.0: A Massive Botnet Infecting Millions of Devices
Today’s top story is the revelation of BADBOX 2.0 , a massive botnet infecting millions of devices. This sophistic...

Cybersecurity Takes Center Stage: A Summary of Top Trends
Cybersecurity takes center stage: there has been a convergence of significant cybersecurity news, highlighting the escal...

Significant Security Events for the Week of Feb. 28th
This report summarizes notable information security incidents affecting businesses globally, focusing on data breaches, ...

A Deep Dive into the Latest Ransomware Scourge: ETHAN
There have been considerable rumblings throughout the cybersecurity community surrounding the emergence of the latest ra...
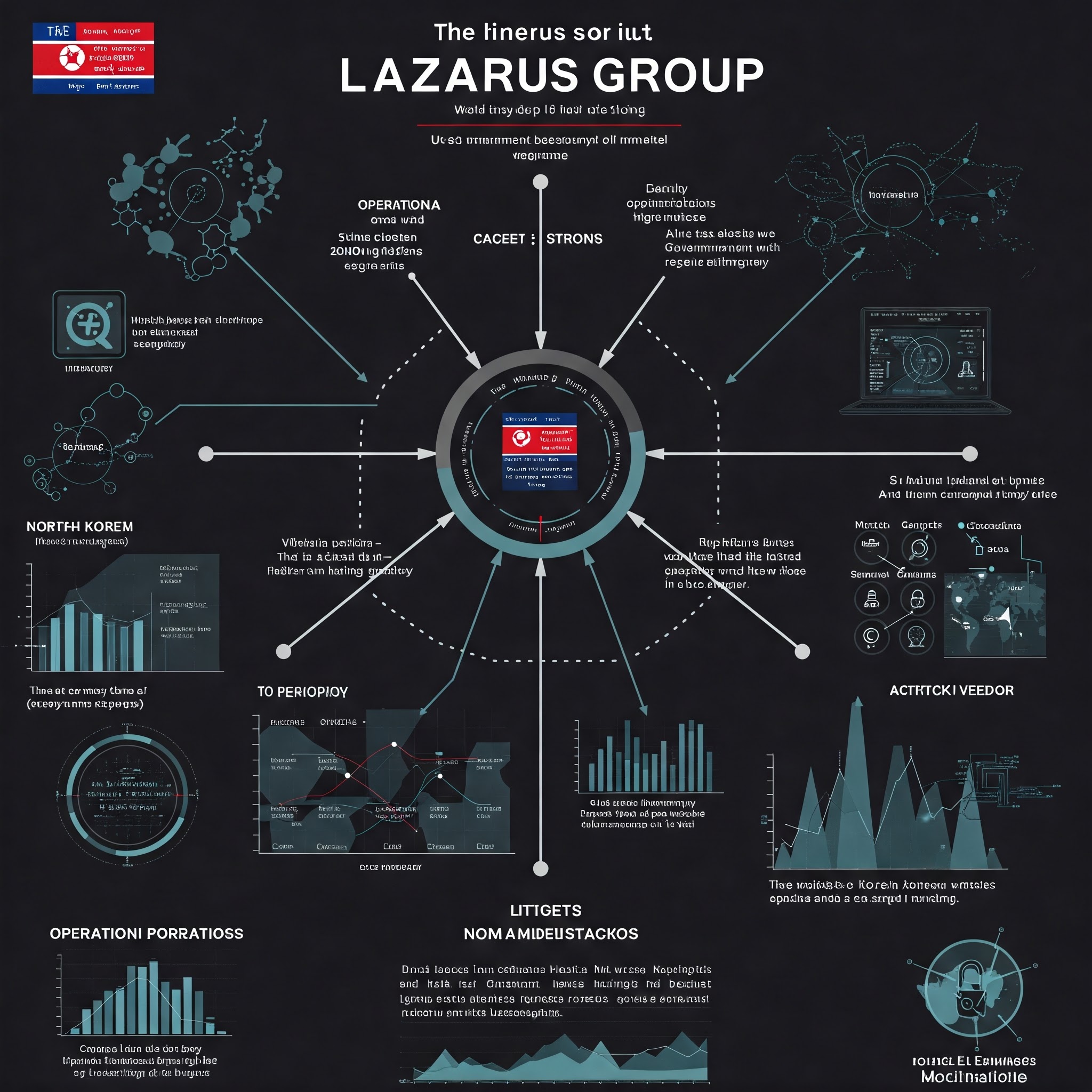
The Lazarus Group's Record-Breaking Crypto Heist: A $1.5 Billion Blow to Bybit
The dominant cybersecurity story today centers around the Lazarus Group, a North Korean state-sponsored hacking group, a...

Gmail Security Upgrade: QR Codes Replace SMS for Enhanced Authentication
Google’s announcement to replace SMS-based two-factor authentication (2FA) for Gmail with QR is a significant shif...

Significant Cybersecurity Incidents of the Past Week.
This week saw a range of significant cybersecurity incidents impacting various sectors, highlighting the persistent and ...

IoT leak exposed a staggering 2.7 Billion records.
This massive breach, dwarfing many previous incidents, exposed a staggering 2.7 billion records, many containing sensiti...

This Week in Cybersecurity: A Critical Review for IT and Security Leaders
This week has seen a concerning rise in various cyber threats, highlighting the persistent and evolving nature of the mo...

Elon Musk's DOGE A Cybersecurity Nightmare?
February 13th, 2025, marked a significant escalation in cybersecurity concerns surrounding Elon Musk’s Department ...
Ban of DeepSeek by Taiwan: A Cybersecurity Wake-Up Call
Today’s dominant cybersecurity story centers around the ban of DeepSeek by Taiwan, citing serious national securit...
A Weekly Analysis for IT Leaders and Cybersecurity Professionals
This week saw a concerning surge in various cybersecurity threats, impacting numerous sectors globally. Key incidents in...

DeepSeek Malware Distributed via Fake Packages. Potential Cybersecurity Crisis
Today’s most significant cybersecurity story revolves around the malicious distribution of DeepSeek malware disgui...

Deepfakes and the $25 Million Heist: A New Era of Cybercrime
The cybersecurity world is buzzing about a disturbingly sophisticated attack that highlights the evolving nature of atta...

The Fall of Major Cybercrime Marketplaces
Today’s most significant cybersecurity news isn’t about a single vulnerability or a specific company breach;...
The Rise of AI-Powered Attacks and the Urgent Need for Enhanced Defenses
The cybersecurity landscape is dominated by a confluence of escalating threats and evolving defensive strategies. The ov...

The Fallout from the Rahman Espionage Case
While several significant cybersecurity events occurred around February 1st, 2025, the most impactful and trending story...

This Week in Cyber: January 25th - 31st, 2025
This week saw a concerning rise in significant cybersecurity incidents impacting various sectors. This analysis is inten...

Disable Local Administrator Accounts to Thwart North Korean Cyber attacks
The most significant cybersecurity story on January 29th, 2025, centers around an urgent warning issued by the FBI regar...
A Multi-pronged Attack Targeting Individuals and Organizations
We have seen a convergence of significant cyber security events, highlighting a multi-front war in cyber security and t...